DNA cryptography: a new French-Japanese approach has proven its worth
| • A French-Japanese team of scientists has developed a cryptographic method that uses DNA as a carrying medium. • DNA has the advantage of generating and sharing large random keys, independently of the distance between the sender and the recipient. • This method provides security that was only thought to be achievable using quantum cryptography. |
Using DNA as a method to encrypt sensitive messages has become possible. A multidisciplinary team has developed a DNA-based encryption approach that can generate and share random keys for encoding messages, regardless of the distance between the sender and recipient. This approach was tested for the first time in real-world conditions during the French President’s visit to Japan1 on 1st April 2026. This research was carried out as part of a collaboration with the CNRS2 , University of Tokyo, Université de Limoges, IMT Atlantique, and the École supérieure de physique et de chimie industrielles de la ville de Paris (ESPCI, Paris PSL), with support from the ANR and France 20303 .The findings will be the subject of a pre-publication in an open archive4
- 1The demonstration will take place during the French President’s visit to the Laboratory for Integrated Micro-Mechatronics Systems (University of Tokyo/CNRS) based in Tokyo.
- 2From the Gulliver Laboratory (CNRS/ESPCI PARIS – PSL). Other scientists from the Laboratory for Integrated Micro-Mechatronics Systems (CNRS/Université de Tokyo) were involved, including Anthony Genot, who served as a project leader, and has since passed away (https://www.insis.cnrs.fr/fr/cnrsinfo/hommage-anthony-genot-une-intelligence-en-resonance-avec-lavenir).
- 3In connection with the MoleculArXiv2 PEPR led by the CNRS and with the ANR DNA Sec project, supported by IMT Atlantique.
- 4This research has not yet been validated by a peer-reviewed scientific journal.
Protecting confidential communications is a central issue of the digital age
Today the encryption of sensitive data mostly relies on “conditional” methods, whose security is based on the assumption that an outside actor does not have sufficient computing power to break the code. “Unconditional” approaches also exist, such as the Vernam Cipher (or OTP, “One-Time Pad” method)5 . While it offers perfect security, in that security does not depend on the adversary’s computing power, this approach imposes multiple constraints: the key used to encrypt the message must be shared beforehand between the sender and recipient. It must also be as long as the content of the message itself, used only once, and “perfectly” random, which is to say impossible to predict. However, generating and sharing single-use long random keys is very difficult with existing methods, especially when the sender and recipient are separated by great distances.
DNA to encrypt messages
That is where DNA becomes interesting. Each DNA molecule consists of four chemical bases (A, T, C, and G), and chemists can commercially synthesise long chains, the base order of which is statistically random. These DNA sequences can then be copied identically via enzymatic processes, and shared between a sender and recipient.
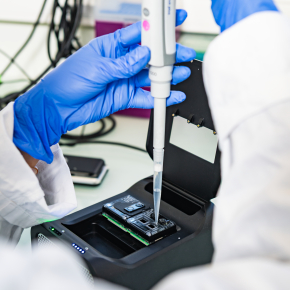
Concretely, scientists prepare duplicate series of DNA - entirely synthetic in origin6 - with one copy kept by the sender, and the other by the recipient. The DNA fragments they contain allow correspondents to generate perfectly random yet identical encryption keys, two by two. This is done immediately before communication thanks to powerful sequencing machines, which read molecules and assemble a binary number key (consisting of 1s and 0s) that can code, send, or decode a message up to a few hundred megabytes.
A reliable, secure, and effective method even at long distance
The strength of this approach is that DNA offers remarkable storage density and stability: correctly conserved, the polymer can remain intact for thousands of years, and only a few milligrams are needed to store exabytes of binary information, the equivalent of a million hard drives. Generating shared DNA-based cryptographic keys has the additional advantage of being independent of the distance between the sender and recipient. In other words, this method could be used between the Earth and the Moon, or beyond.
Above all, this DNA-based approach renders accessible the only cryptographic method that can be mathematically proven to offer unconditional security, which is to say one that is independent of the adversary’s computing power. By testing different scenarios, scientists showed that even if the DNA used to generate keys were intercepted, the channel would remain inviolable, because there are only two copies of each DNA sequence – one for the sender and another for the recipient – and any partially stolen key would never be used again by the correspondents. Similarly, if the interceptor tried to amplify the key to obtain multiple copies before returning it to the users, this operation would result in anomalies in the number of copies, which would be detectable by the correspondents, who would subsequently no longer use those keys.
Thanks to its multiple advantages and reliability, this approach opens new avenues for protecting the most sensitive communications – whether diplomatic, military, or scientific. Over the long-term, it could also find applications in extreme contexts, such as space communications or critical digital infrastructure, where the reliability and inviolability of communications are crucial.
Ressources :
CNRS video : https://www.youtube.com/watch?v=M1U8zkYX1II
Interview with Bruno Le Pioufle, new Director of the Northeast Asia Representative Office : https://www.cnrs.fr/fr/actualite/lassociation-du-japon-horizon-europe-ouvre-de-nouvelles-perspectives-la-recherche
- 5Vernam Cipher, or the “one-time pad” (OTP) method, is a symmetric encryption system based on a single-use random key that is as long as the message. When applied correctly, it offers theoretically perfect security, for the encrypted message reveals no information without the key.
- 6The DNA used in cryptography is based on a synthetic production process inspired by principle of DNA coding; there is no biological, functional, or genetic link to the DNA of living organisms.
Synchronized DNA sources for unconditionally secure cryptography. Sandra Jaudou*, Hélène Gasnier*, Elias Boudjella*, Marc Canève, Victoria Bloquert, Vasily Shenshin, Tilio Pilet, Sacha Gaucher, Soo Hyeon Kim, Philippe Gaborit, Gouenou Coatrieux, Matthieu Labousse, Anthony Genot, and Yannick Rondelez. * equivalent contributions
HAL link : https://hal.science/hal-05560338